Using IP flow verify
In this demonstration, we are going to use IP flow verify to test the connection between two of the VMs that we created in the first demonstration. To use IP flow verify, perform the following steps:
- Inside the Network Watcher resource blade, under the Network diagnostic tools context, select IP flow verify.
2. On the settings page, add the following settings:
- Resource group: AZ104-NetworkWatcher.
- Virtual machine: networkwatcher1.
- Network interface: This will be filled in automatically after selecting the VM.
- Protocol: TCP
- Direction: Outbound
- Local IP address: This is filled in automatically as well.
- Local port: 60000.
- Remote IP address: 13.107.21.200 (a Bing server IP address).
- Remote port: 80.
- Click the Check button and notice the successful result.
- The request is executed and the result it will return will be that access is allowed, because of the AllowInternetOutBound security rule, as shown in the following screenshot:
Figure 18.27 – AllowInternetOutBound
- Repeat the actions up to Step 3 again, and this time, make the following changes:
• Direction: Inbound
- This will result in the following, which is denied because of theDenyAllInBound rule:
Figure 18.28 – DenyAllInBound
We’ve looked at how to use IP flow verify to test the connection between two of the VMs.
In the next part, we are going to look at effective security rules.
Effective security rules
The effective security rules feature displays all the security rules that are applied to the network interface and the subnet where the network interface is. It then aggregates both. This will give you a complete overview of all the rules that are applied to a network interface, and it will give you the ability to change, add, or remove rules. You need to select the right subscription, the resource group, and the VM to get an overview of the applied security rules, as shown in the following screenshot:
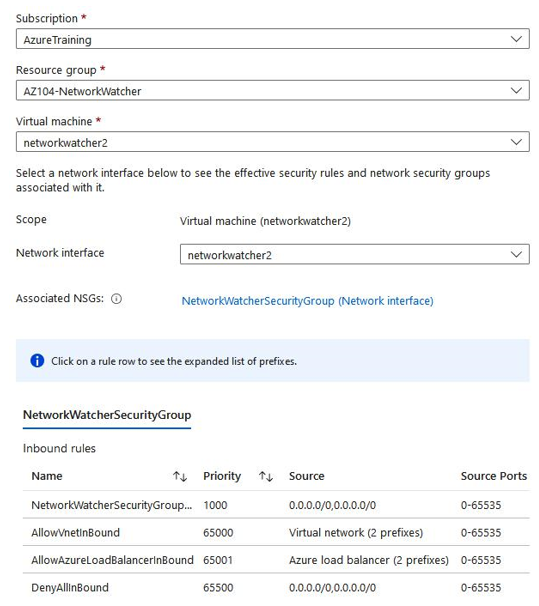
Figure 18.29 – Network Watcher, effective security rules
We’ve now seen an overview of the security rules that are applied to the network interface.
In the next section, we are going to cover connection troubleshoot.